28 December 2021 — True Publica

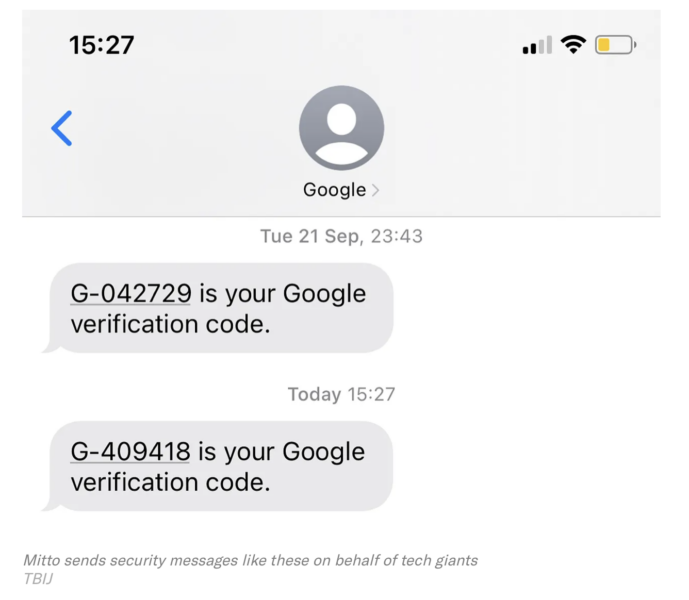
By Crofton Black: Need to verify your identity on a phone? Reset a password? Log in to a sensitive site or account? You’ll probably get a text message to check who you are. But it won’t come directly from your account provider. Instead, it will come via one or more middlemen: little-known bulk messaging companies that use the access they’ve brokered to hundreds of phone networks to send millions of messages cheaply and quickly around the world.
But this efficiency comes at a cost.
Today, with Bloomberg News, the Bureau revealed how the chief operations officer of a prominent messaging company – Mitto AG – allegedly became a facilitator for the surveillance industry.
Overtly, Mitto works for some of big tech’s most prominent names, helping them to send millions of text messages to phones worldwide. Covertly, its network access is claimed to have been opened up by its COO to the spy industry so that end users – government customers, the Bureau is told – could locate and track persons of interest
As the Pegasus Project emphasised earlier this year, the global trade in spy tech is out of control. While the companies that build these tools say that they are only used by governments to target serious criminals, more and more data has emerged to show that this is wide of the mark. Mitto’s networks were used to target a senior US government official. And last year the Bureau showed how telecom networks subleased by Rayzone Group targeted a fleeing Emirati princess. The Pegasus Project counted journalists, activists and politicians among the people surveilled. The old explanation that this tech is only ever used to find terrorists, drug barons and paedophiles no longer holds water.
“Cyber warfare against mobile phone users is now pervasive and will only get worse,” Brian Collins, CEO of AdaptiveMobile Security, a telecom security company, told The Bureau. “The mobile phone and related services have become the target for every criminal, fraudster and nation state out there.”
Recent headlines have focused on NSO Group, which has been under pressure from US sanctions as well as lawsuits from WhatsApp and Apple and has also been accused of targeting US government officials. But the revelations about its activities expose the tip of an iceberg. Dozens of government agencies around the world, including those of repressive and authoritarian regimes, rely on corporate surveillance as a service: high-tech companies that offer phone tracking, message intercepts, social media mining and hacking.
These high-end surveillance companies, which sell their services to governments for millions of dollars, can only function thanks to intermediaries: the enablers inside the telecom industry. Last year the Bureau revealed how spy companies bought access from mobile phone operators in the UK and across the world, leasing their network connections, known as global titles. In theory, national regulators should always know which company is using which global title at any time. In practice, it’s a murky world of subcontracting with access often being sold on, sometimes at several removes from its nominal owner.
But paying for individual global titles is risky for high-end firms. Phone companies can, and do, shut down connections when they notice malicious traffic. So spy firms need spares – fresh access points that they can turn to when one gets burnt.
There is another complicating factor. Using mobile phone networks to locate people and potentially intercept their messages relies on the dark arts of SS7 signalling, which finds routes into different networks around the world. These routes are hard to navigate: phone operators and security firms play cat and mouse with spy companies and spammers. The solution for those attacking the networks is to have a lot of access points in different places, since you might never know which one will connect to your target most effectively.
Enter Mitto. Using a bulk messaging company – or aggregator, as they are called in the trade – neatly solves both of these problems. Aggregators have a truly global reach, with hundreds of network access points. And they send millions of messages a day, which means that any surveillance traffic they carry may be barely discernible within their legitimate business.
From spamming to spying
Bulk messaging today has its roots in the spam industry. In theory, if you want to send a text message to another network’s subscriber, you make a deal with that network and pay an associated cost: up to a few pennies per message. So if you want to send a million messages offering cheap pharmaceuticals or cut-price luxury watches, that’s a cost of £10,000-£50,000.
But what if you send the messages without having an agreement? The network may just let them in anyway. Or what if you send them, but, as some companies did, make it look as if they came from somewhere else – say, from another operator who would later get the bill? (It is not suggested Mitto did this.)
“Nobody ever dreamt of SMS becoming so big,” Tobias Engel, a security researcher, told The Bureau. “As a consequence, there was no protection at all against bypassing charging mechanisms. This attracted many shady actors who were quickly able to grow their businesses in the booming SMS industry. It was like printing money: charge your customers for every single message, but don’t pay the networks you are sending to.”
The fact that these scams worked led to a flourishing market where spammers could make millions of dollars from unprotected or badly protected phone operators. Some companies emerged as masters of “grey routing” – finding ways around operators’ protections to send more messages even more cheaply. Eventually operators would catch on, but this didn’t mean the end of the spamming business. Instead, it was parlayed into legitimacy.
On the one hand, bulk message senders, when caught, made agreements with the operators – both parties now got a cut, and the former spammer got an additional access point that it could use to send more messages. On the other hand, the global growth of mobile internet services offered an opportunity for the aggregators to handle legitimate traffic.
As more people got smartphones and started using email, social media, banking and other services on them, SMS became a handy way for internet giants to verify their customers’ accounts. If you forget your password, or need to authorise a transaction, it is likely that your access can be restored via SMS. In many ways, SMS has become the key to identity in the digital realm – not because it is trusted, but because it is quick, convenient, and cheap.
Few people outside the industry will have heard of Mitto and its competitors in bulk messaging. But equally few would be able to access their essential online services without them.
The revelation that someone at one of these businesses could help enable intrusive surveillance for several years while also working for the world’s largest internet companies raises important questions about trust and security in our online ecosystem. What kind of due diligence should tech giants carry out on their service providers – especially when these service providers are carrying out critical security functions?
“There can be multiple middle-men between the company which offers the SMS service and the company which actually sends it,” Engel pointed out. “And everyone in between is trying to make more money by using the cheapest route available to them.”
Collins warned: “Unless a coherent and concerted effort is made at government level in concert with the carriers, aggregators and phone manufacturers, confidence in mobile telecommunication networks will be completely eroded. Services and privacy will be constantly undermined.”
Crofton Black is a writer and researcher specialising in technology and security. He is a leading expert on the CIA’s rendition, detention and interrogation programme and a specialist in military and intelligence corporate contracting.
Leave a comment